One of the most crucial aspects of keeping your cryptocurrency safe is ensuring that your private key is out of reach and out of harm’s way. It is usually recommended that you avoid keeping it in any device such as a computer, whose security can be compromised by malware.
[no_toc]Hardware wallets are said to be among the most secure storage options for your cryptocurrency. They are a cold storage solution that offers matchless security for your crypto funds.
How do they work? How can they achieve this level of security? Read on to find out everything you need to know about hardware wallets.
Best Hardware Wallet Providers
Best Hardware Wallets in Your Country

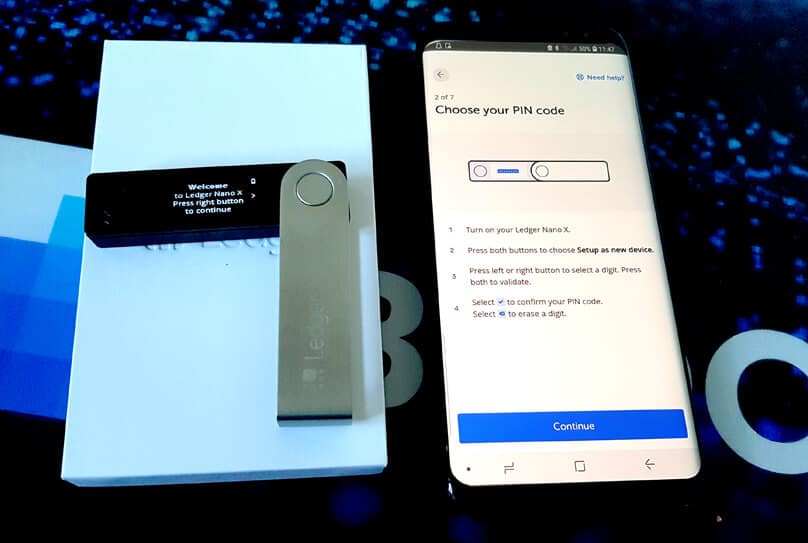
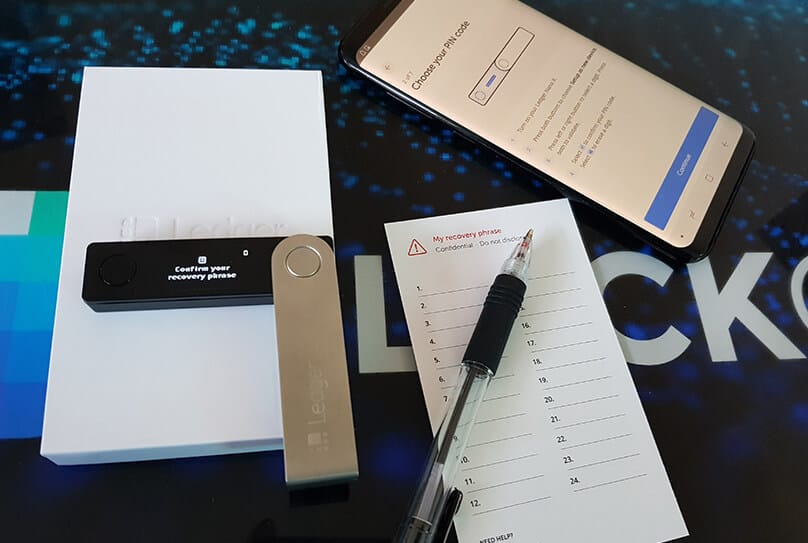
There are numerous hardware wallets for users in the UK. However, one of our top picks is the Ledger Nano X. What makes it a great choice is the fact that it is the only hardware wallet with Bluetooth support.
This means that you can use the wallet to transact without having to connect it to a PC. In the current era, this level of convenience is far more important than a majority of other features.
A great choice of hardware wallets for US and Canada residents is the Ledger Nano S. It offers support for a much wider range of cryptocurrencies than any other hardware wallet.
In fact, it is the only hardware wallet which supports Ripple (XRP).

For residents of Australia, both the Ledger Nano S and the Ledger Nano X are great options. They support the most coins and offer lots of versatility.
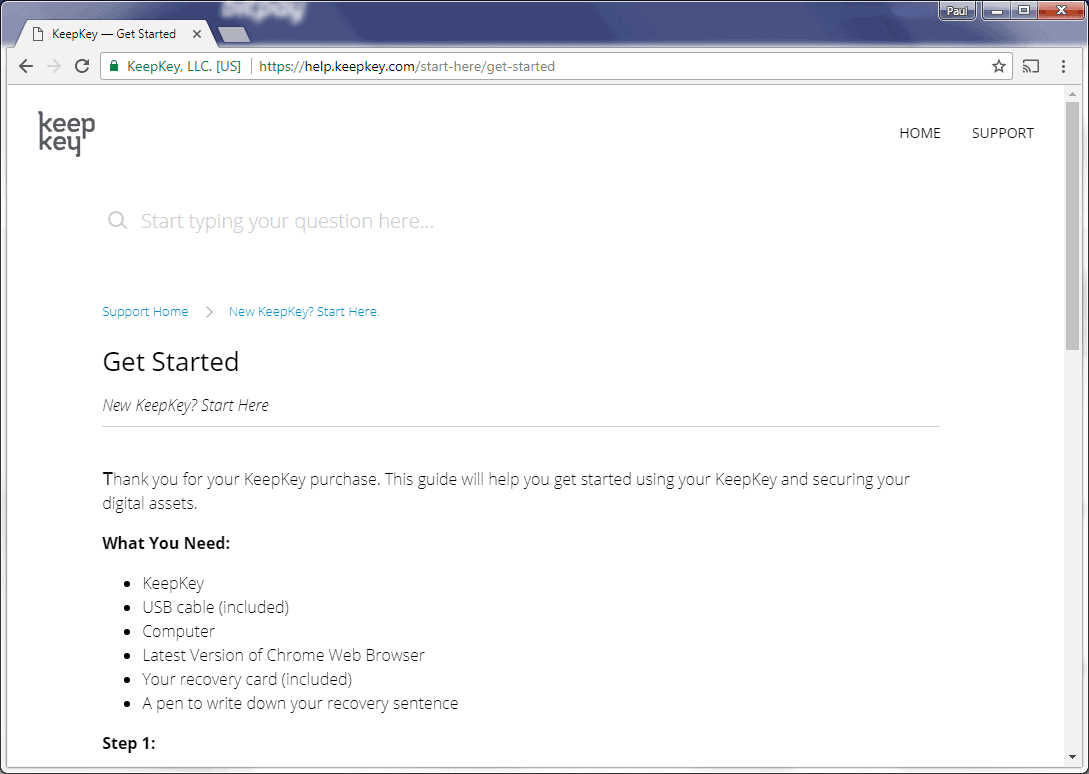
But for a user whose main interest is functionality, KeepKey would also fit the bill perfectly. It is one of the few hardware wallets whose screen offers the most convenience in terms of size and visibility.
Differences Between Exchange, Hardware and Software Crypto Wallets
Though this review has focused on hardware wallets, there are a number of other different types of wallets. Let us analyze these different types:
Exchange Wallets
On crypto exchanges, users have access to hot wallets maintained by the exchange service provider. These offer storage facilities for coins after purchase and when trading.
However, by virtue of the fact that they are always online, they are the least secure storage option for your crypto needs. Use an exchange wallet only for short term storage and transfer your funds to cold storage as soon as possible to avoid losing funds to hackers.
Here are our favorite exchange wallets:
- Binance Wallet
- Coinbase Wallet

Hardware Wallets
As discussed above, this type of wallet offers the most safety for users funds as they make use of cold storage. They are ideal for long-term storage of crypto funds or even temporary storage of big amounts.
All hardware wallets are safe and only differ in convenience and usage. But make sure you only buy from the authorized distributor to avoid getting counterfeit items.
Here are some good examples of hardware wallets:
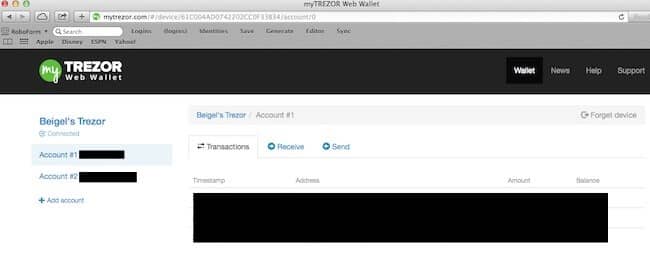
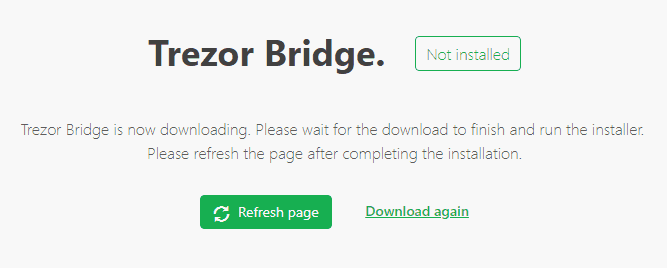
- Ledger Nano S
- Trezor
- KeepKey
Software Wallets
Software wallets are essentially apps that store crypto on your PC or phone. Though they are safer than exchanges, they are still vulnerable to hacking because they are online.
They are ideal for everyday use but not for long-term storage.
Here are some good examples of software wallets:
- Coinomi
- Exodus
- MyEtherWallet
Best Wallet on Mobile
In the present day, a majority of crypto users consider convenient access to funds as one of the top priorities. For this reason, mobile wallets are among the most popular forms of storage. But which one is the best?
There are tons of viable options when choosing a hardware cryptocurrency wallet. To make the right choice however, you need to weigh some important considerations.
One of these is the variety of coins that different wallets support. If you use multiple cryptocurrencies, you would need a wallet that supports a good number of them.
Another aspect has to do with personal preferences. As you might have noticed, each of the wallets discussed above differs in design and features from the rest. If portability matters more to you than any other feature, you might want to pick the smallest or lightest.
But if functionality is your key focus, you might want to choose the one with the highest usability in terms of design.
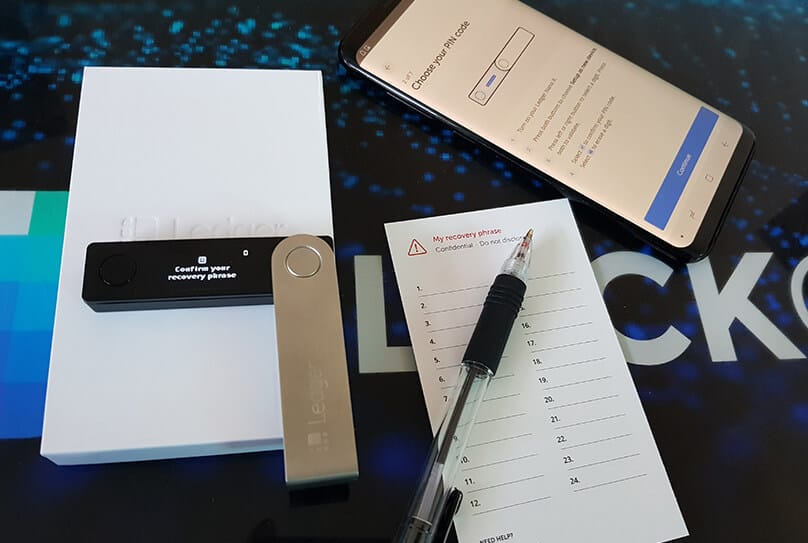
All in all, remember that the security of your funds will depend on how well you keep your device, its PIN code and recovery phrase. Observing the required security requirements will keep your funds out of harm’s way.
FAQs
What will happen to my funds if I lose my hardware wallet or if it gets damaged?
You can restore your funds using the seed key that you generated during the initialization process when setting up your device. In order to do this, you can order for another device or use a compatible crypto wallet such as Electrum or Mycelium.
What happens if I forget my device PIN code?
To reset your PIN, you can restore factory settings and then recover your wallet using the 24-word seed phrase.
Can I use a USB flash drive in place of a hardware wallet?
No. A USB flash drive cannot replace a hardware wallet as it lacks the specialized architecture of the latter for offline storage and random private key generation.
What happens when someone steals my hardware wallet?
Every hardware wallet makes use of a unique PIN code to restrict access to authorized users. For someone to use the wallet to access your funds they would require either this PIN or your recovery seed.
Are there any known successful attacks against hardware wallets?
It is possible that a physically captured device could get hacked by tech-proficient attackers. But such instances are extremely rare.
Is it wrong to buy hardware wallets from online stores such as eBay?
It is risky to buy your hardware wallet from any other source other than the original manufacturer or an authorized distributor. There have been instances when people have bougth pre-initialized or counterfeit items by so-called resellers.