Join Our Telegram channel to stay up to date on breaking news coverage
A newly published research suggests that attackers have found vulnerabilities in the Tor browser. This vulnerability may have allowed attackers to steal Bitcoin from the users.
Tor vulnerability found
Nusenu, who discovered this attack, said that Tor might not be such a good choice after all. It usually protects anonymity by routing the data through several relays. The Tor browser is very popular amongst people using Dark Web. Several people in the crypto community also use Tor to ensure the safety and anonymity of their Bitcoin transactions.
The browser was developed by the US government for anonymizing internet communication and has become a popular tool among privacy advocates. However, nusenu suggests that the exit relays on Tor are the last hop in the process of routing data through different relays. These exit relays are the only places where the actual destination of a Tor user is available.
Malicious parties use exit relays
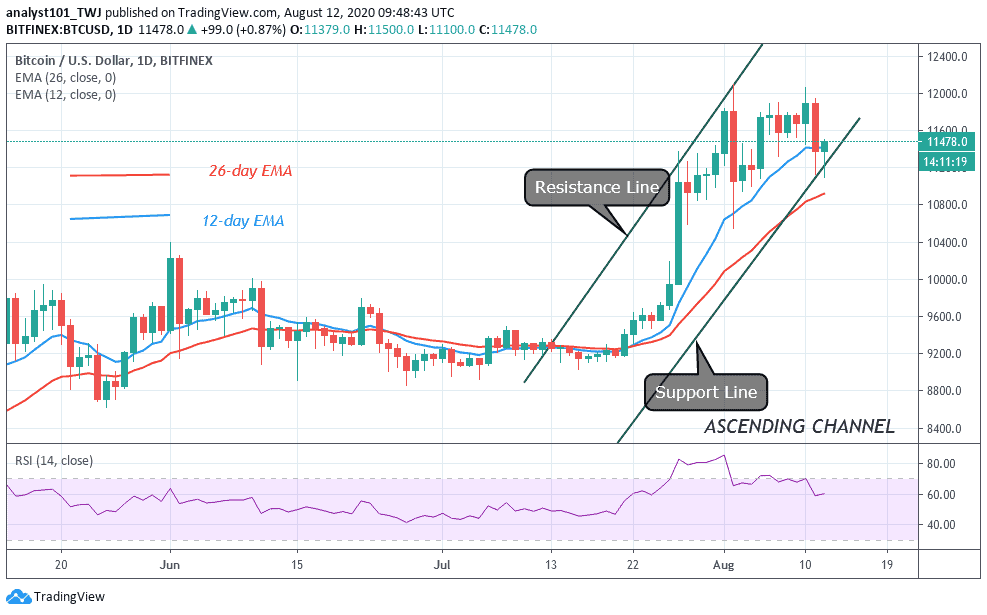
In January this year, a malicious actor began running a large number of exit relays on the network which peaked at about 23% in May. These relays performed the “person-in-the-middle” attack on the system.
More specifically,
“They perform person-in-the-middle attacks on Tor users by manipulating traffic as it flows through their exit relays. They (selectively) remove HTTP-to-HTTPS redirects to gain full access to plain unencrypted HTTP traffic without causing TLS certificate warnings.”
This is a previously known vulnerability in the system and comes with countermeasures as well. However, they are not always adopted by websites. Nusenu suggests that the attackers were focused majorly on crypto related websites. They would route transactions to their own Bitcoin addresses. They specifically targeted multiple Bitcoin mixer services.
In August, the number of relays that the hacker controlled went down to about 10%. However, the researcher informed that they cannot suggest the amount of Bitcoin stolen by hackers because of the vulnerability.
Join Our Telegram channel to stay up to date on breaking news coverage