On this Page:
Cryptocurrency scams have reached alarming new heights. The Federal Bureau of Investigation reported that in 2023 alone, losses from cryptocurrency fraud exceeded $5.6 billion, approximately half of all reported fraud losses. As cryptocurrency prices grow and become more important in the world economy, scammers are developing newer and more devious methods of their own.
While traditional financial systems have established customer protections, cryptocurrency’s decentralized nature creates a fertile environment for fraudsters. Understanding crypto scams and how they work could be the difference between building wealth and losing everything.
In this guide, we explore the most common cryptocurrency scams, recall some of the most famous examples, and offer practical steps to protect yourself.
Key Takeaways
- The irreversible character of blockchain transactions and limited regulations make crypto an attractive target for fraudsters.
- Common scam types include investment frauds, phishing attacks targeting wallet credentials, and social engineering scams that exploit trust.
- Protect yourself by using established exchanges with strong security, enabling 2FA, keeping private keys secure offline, and thoroughly researching projects before investing. Recognizing red flags like guaranteed returns and pressure tactics is essential.
What Are Crypto Scams?
Crypto scams are fraudulent schemes created to steal cryptocurrency or personal information. Scammers choose to target crypto investors for a number of reasons:
- Transactions are irreversible. Unlike credit card transactions or bank transfers, cryptocurrency transactions cannot be reversed once confirmed on the blockchain. When your crypto is gone, it’s usually gone for good.
- Regulations are limited. The cryptocurrency market lacks the regulatory frameworks that protect consumers in traditional financial markets. Obviously, this is an opportunity for scammers.
- The issue of anonymity. While blockchain transactions are publicly recorded, the identities behind wallet addresses can remain anonymous, making it difficult to track down perpetrators.
- Technical complexity creates obstacles. Many people don’t fully understand blockchain technology or how cryptocurrencies work. That’s why scammers can easily create convincing technical jargon to mask fraudulent schemes.
- FOMO (Fear of Missing Out) is a factor. Stories of overnight crypto millionaires create a powerful emotional motivation that scammers exploit, pushing victims to act quickly without due diligence.
Common Characteristics of Crypto Scams
Despite their variety, most cryptocurrency scams share several warning signs. Be attentive when you recognize these patterns:
- Promises of guaranteed returns or “risk-free” investments
- Pressure to act quickly or miss out on an opportunity
- Requests to share private keys or wallet seed phrases
- Anonymous or unverifiable team members
- Poor quality documentation and communications
- Excessive marketing with little substance about the technology
- False claims of celebrity endorsements or partnerships with well-known companies
One of these characteristics does not necessarily mean the coin is a scam, but if it ticks several boxes, you’re better off avoiding it.
Types of Crypto Scams
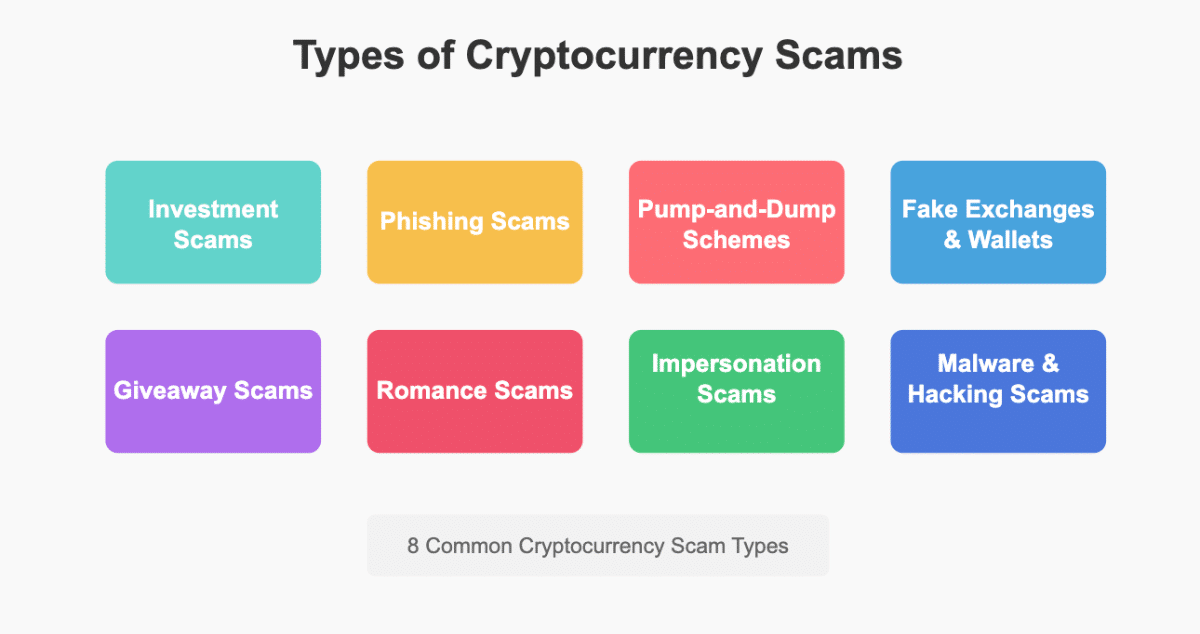
In this section, we discuss common types of scams. Some fraudsters are original in their deviousness, while others follow more established patterns.
Investment Scams
Investment scams are the most reported type of cryptocurrency fraud, according to the FBI, and they come in several forms:
Ponzi and Pyramid Schemes
Crypto Ponzi schemes pay early investors with funds from new investors, creating an illusion of legitimacy and profitability until the scheme collapses.
Similarly, pyramid schemes in cryptocurrency often disguise themselves as legitimate multi-level marketing (MLM) operations. Participants are motivated to recruit new members, with commissions flowing upward through the organizational structure. While MLM itself isn’t illegal, when there’s no legitimate product or service, just recruitment, it becomes a fraudulent pyramid scheme.
Fake Initial Coin Offerings (ICOs)
In an ICO, a company creates a new cryptocurrency token and sells it to raise funds for a project. Scammers exploit this model by creating fake ICOs with impressive-sounding white papers and flashy websites, but with no intention of developing an actual product. After raising funds, the scammers disappear with investors’ money.
Legitimate ICOs provide detailed technical documentation, have verifiable team members with relevant experience, and transparent roadmaps. Fake ICOs typically emphasize marketing over substance and create artificial urgency to pressure investors.
The European parliament website provides a short summary of what a legitimate ICO should consist of.
Rug Pulls
A “rug pull” happens when cryptocurrency developers abandon a project and run away with investor funds. Typically, scammers create a new token, drive up the price through false announcements and artificial hype, and then sell all their holdings at once, draining the liquidity and leaving investors with worthless tokens.
Phishing Scams
Phishing remains one of the most common methods for stealing cryptocurrency, targeting the private keys that control access to digital wallets.
Fake Websites and Login Pages
Scammers create convincing replicas of popular crypto exchanges or wallet interfaces. When users enter their login credentials on these fake sites, the information is immediately captured by scammers who use it to access the genuine accounts and steal funds.
These sites often have URLs that closely resemble legitimate platforms, perhaps with a subtle misspelling or additional character that might go unnoticed at a glance.
Email and Social Media Phishing
Phishing attacks often begin with emails or messages that appear to come from legitimate cryptocurrency companies. These communications usually create a sense of urgency, claiming your account has been compromised or needs verification, and include links to fake websites designed to steal your credentials.
According to the FBI, over 300,000 people fell victim to phishing scams in 2022, collectively losing over $52 million.
Pump-and-Dump Schemes
Pump-and-dump schemes involve artificially inflating the price of a cryptocurrency (the “pump”) before selling off holdings at the higher price (the “dump”), leaving other investors with devalued assets.
Scammers typically target low-market-cap cryptocurrencies that are easier to manipulate. They purchase large amounts of the chosen coin, then use social media, messaging apps, and fake news to create excitement and encourage others to buy in, driving up the price. When the price reaches a target, the scammers sell their entire holdings, causing the price to collapse.
Social media influencers sometimes participate in pump-and-dump schemes by promoting specific cryptocurrencies to their followers without disclosing that they’re being paid to do so or that they plan to sell their holdings once the price rises.
Fake Exchanges and Wallets
Fraudulent exchanges initially work like legitimate platforms, allowing users to deposit funds and even make small withdrawals to build trust. However, these exchanges may suddenly shut down, claiming to be “hacked” or experiencing “technical difficulties,” effectively stealing all user deposits.
These fake exchanges often attract users with unrealistically low fees or extravagant promotional offers, and they typically lack proper licensing, regulation, and security measures. They may also manipulate trading volumes and prices to create various illusions of a market.
Malicious Wallet Apps
Scammers create counterfeit versions of legitimate cryptocurrency wallet applications and distribute them through unofficial channels or sometimes even through official app stores. These fake wallets are created to steal your private keys and transfer your funds to the scammers’ addresses as soon as you deposit cryptocurrency.
To protect yourself, only download wallet applications directly from the official website of the wallet provider or from official app stores after carefully verifying the developer’s identity.
Giveaway Scams
In fake celebrity giveaway schemes, scammers impersonating well-known figures or popular celebrities will announce a crypto giveaway that requires users to first send a small amount of cryptocurrency to verify their address, promising to return multiple times the amount sent. Naturally, victims who send cryptocurrency never receive anything in return.
These scams use trust in celebrities and create a sense of urgency with limited-time offers. They often present elaborate stories to justify the giveaway, such as “giving back to the community” or celebrating a milestone. The scammers might also use deepfake technology to create convincing videos of celebrities announcing these fake promotions.
Romance Scams (“Pig Butchering”)
In these scenarios, fraudsters create fake profiles on dating apps or social media and develop seemingly genuine romantic relationships with their targets. Over time, they introduce the topic of cryptocurrency investments, often claiming to have insider knowledge or access to exclusive investment opportunities.
Once trust is established, the scammer encourages the victim to invest in a “special” trading platform that shows fabricated profits. Victims can often withdraw small amounts initially, building further confidence that leads them to invest bigger sums. When the victim attempts to withdraw a large amount, the platform suddenly requires additional “fees,” “taxes,” or “verification payments,” or simply becomes inaccessible.
The term “pig butchering” comes from the scammer’s strategy of “fattening up” victims with false profits before the final “slaughter”—taking all their investments. The FBI reported that in 2022, victims lost over $735 million to romance scams.
Impersonation Scams
Scammers monitor social media for users reporting problems with cryptocurrency platforms, then approach them posing as customer support representatives. These fake agents direct victims to phishing websites or request private information like passwords and private keys, claiming they need this information to resolve the issue.
Legitimate companies will never ask for your private keys or seed phrases. Their customer support typically communicates through official channels, not via direct messages on social media.
Scammers Posing as Government Agencies or Authorities
In these schemes, fraudsters impersonate government officials, claim legal problems or frozen accounts due to investigations, and pressure victims to transfer cryptocurrency to “protect” their funds. Some scammers stay on the phone with victims, guiding them through the process of converting money to cryptocurrency at ATMs and sending it to the scammer’s wallet.
The FBI reported that in many cases, scammers direct victims to specific Bitcoin ATMs and guide them through the process of depositing cash and transferring the purchased Bitcoin to the scammer’s wallet.
Malware and Hacking Scams
Crypto-jacking involves secretly installing malware on a victim’s device that uses their computing resources to mine cryptocurrency for the attacker. This type of attack can slow down devices, increase electricity costs, and potentially expose sensitive information to hackers.
The malware is typically distributed through phishing emails, compromised websites, or infected software downloads. Users might notice their devices running unusually hot or slow as the hidden mining software consumes processing power.
Clipboard Hijacking (Modifying Wallet Addresses)
This attack involves malware that monitors a user’s clipboard for cryptocurrency wallet addresses. When the user copies a wallet address to make a transaction, the malware automatically replaces it with the scammer’s address. Unless the user carefully verifies the entire address before confirming the transaction, their funds will be sent to the attacker instead of the intended recipient.
Real-World Examples of Crypto Scams
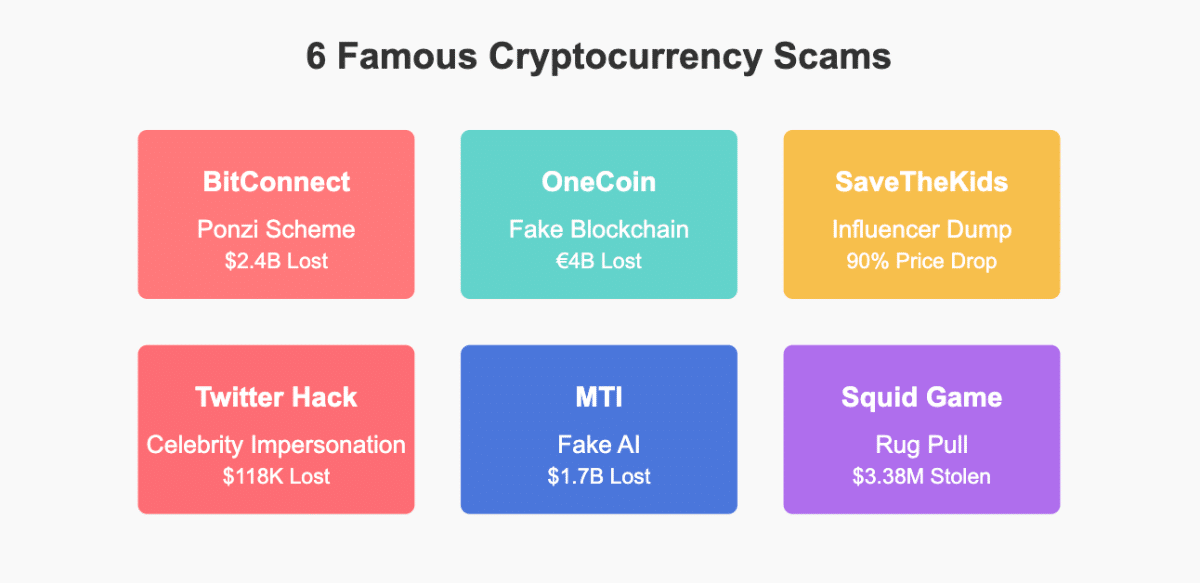
All these theory might seem overwhelming, so let’s see in practice how some famous scams took place throughout the years.
1. Bitconnect (2016–2018) – Ponzi Scheme
Bitconnect was one of the largest cryptocurrency Ponzi schemes in history. The platform promised investors daily returns of up to 1% through a proprietary “trading bot” and used a multi-level marketing structure to attract new investors.
In reality, BitConnect was a classic Ponzi scheme where no actual trading bot existed, early investors were paid using funds from new investors, and a multi-level marketing structure (with 7-tier referral commissions) motivated victims to recruit others.
At its peak in December 2017, Bitconnect had a market capitalization of over $2.6 billion. However, in January 2018, the platform suddenly closed, converting all users’ investments into Bitconnect Coin (BCC), which rapidly crashed in value. Investors lost an estimated $2.4 billion.
In February 2022, the U.S. Department of Justice indicted the founder, Satish Kumbhani, on charges including conspiracy to commit wire fraud, commodity price manipulation, and money laundering. If convicted on all counts, he faces up to 70 years in prison.
2. OneCoin (2014–2019) – Fake Cryptocurrency
OneCoin, founded by self-proclaimed “Cryptoqueen” Ruja Ignatova, collected over €4 billion from investors worldwide. The company claimed to be a legitimate cryptocurrency with its own blockchain, but investigators later discovered it had no blockchain at all—just a centralized SQL database controlled by the company.
OneCoin collected over €4 billion from investors worldwide, with many people losing their entire life savings to the scam. It used technical jargon to confuse investors about blockchain technology, and operated through a multi-level marketing structure to expand rapidly.
In 2017, Ignatova disappeared after a U.S. warrant was issued for her arrest. Her brother, Konstantin Ignatov, took over the company but was arrested in March 2019 and charged with wire fraud, securities fraud, and money laundering.
Despite the arrest of key figures, many victims have never recovered their funds, and Ignatova remains one of the most wanted fugitives in the world.

3. SaveTheKids Token (2021) – Pump-and-Dump Scheme
The SaveTheKids token scam was a classic pump-and-dump scheme with a modern twist. Launched in June 2021 with promotion from popular social media influencers, it claimed charitable purpose – that a percentage of transaction fees would go to children’s charities.
SaveTheKids token created artificial demand and hype through coordinated influencer marketing, but shortly after launch, the promoting influencers secretly sold their pre-allocated tokens. This mass selling caused the price to crash by over 90%, leaving regular investors with worthless tokens.
The backlash led several platforms to update their cryptocurrency promotion policies to highlight the dangers of celebrity-endorsed crypto projects.
4. Twitter Bitcoin Scam (2020) – Celebrity Impersonation
In July 2020, a group of hackers led by Florida teenager Graham Ivan Clark gained access to Twitter’s internal systems and compromised high-profile accounts including those of Barack Obama, Joe Biden, Elon Musk, Bill Gates, and Apple. The compromised accounts tweeted similar messages promising to double any Bitcoin sent to a specific address.
Within hours, the scammers had received over 400 payments totaling more than $118,000. Clark was identified as the main perpetrator and sentenced to three years in prison after pleading guilty to the hack.
Even verified social media accounts can be compromised and used for cryptocurrency scams. A healthy dose of skepticism is important toward any investment opportunity that seems too good to be true, regardless of the apparent source.
5. Mirror Trading International (MTI) (2019–2020) – Fake Trading Platform
Mirror Trading International claimed to use AI trading software to generate consistent returns for Bitcoin investors. By 2020, MTI had attracted approximately 280,000 investors from around the world who deposited at least 29,000 Bitcoin (worth approximately $1.7 billion at the time).
In December 2020, the company’s CEO, Johann Steynberg, disappeared, and MTI stopped processing withdrawals. Subsequent investigations revealed no evidence of legitimate trading and concluded that MTI operated as a Ponzi scheme. The company was placed into final liquidation by the Western Cape High Court in South Africa.
Though MTI was headquartered in South Africa, its victims were spread across more than 170 countries, complicating recovery efforts.
6. Squid Game Token (2021) – Rug Pull
Capitalizing on the popularity of Netflix’s “Squid Game” series, developers launched the SQUID cryptocurrency in October 2021. The token was marketed as an entry point to a play-to-earn game based on the show, though no official connection to Netflix existed. Red flags included a website filled with spelling errors, fake team members using photos stolen from other websites, and the inability to sell tokens, but tokens sold like hot cakes regardless.
Within days, the token’s price surged from $0.01 to over $2,800. However, investors soon discovered they couldn’t sell their tokens due to “anti-dumping technology” in the smart contract. On November 1, 2021, the developers sold all their holdings and disappeared, causing the price to crash to nearly zero and stealing an estimated $3.38 million from investors.
How to Stay Safe from Crypto Scams
After understanding what types of methods scammers generally use, it is equally important to know how to avoid and stay safe from these fraudsters.
Learn to Identify Red Flags
Legitimate investments always involve risk, and anyone promising guaranteed profits is likely running a scam. Cryptocurrencies are particularly volatile, and their prices can fluctuate dramatically over short periods. Be especially wary when you hear claims like “10% daily returns” or “double your money in a week.”
Scammers often create artificial urgency to prevent potential victims from researching or thinking critically about an investment opportunity. If someone tells you phrases like “limited-time offer,” “last chance,” or “act now before it’s too late”, it should be a trigger for immediate skepticism.
Remember that legitimate cryptocurrency projects provide clear information about:
- Who the team members are, with verifiable backgrounds.
- How the technology works, often with publicly available code.
- The tokenomics (how the cryptocurrency is distributed and managed).
- Regular updates on development progress.
When this information is missing, vague, or difficult to verify, proceed with extreme caution.
Protect Your Crypto Assets
Stick to established cryptocurrency exchanges with strong security records and regulatory compliance. Major platforms like Coinbase, Binance, Kraken, and Gemini have invested heavily in security measures and insurance against certain types of losses.
For storing cryptocurrency, consider hardware wallets like Ledger or Trezor for larger amounts, as they keep your private keys offline and protected from online attacks. For smaller amounts or frequent trading, use reputable software wallets from established companies.
Our page on buying and storing cryptocurrency has everything to need to know about protecting your investments.
Enabling 2FA
Always enable two-factor authentication on all your cryptocurrency accounts. Authenticator apps like Google Authenticator or Authy provide more security than SMS-based authentication, which can be compromised through SIM-swapping attacks.
Many exchanges now support hardware security keys like YubiKey, which offer even stronger protection against phishing attempts, as they verify the website’s identity before submitting authentication codes.
Keeping Private Keys Secure
Your private keys are the only way to access your cryptocurrency. Never share them with anyone, and store them securely offline, preferably in multiple secure locations. Consider using a secure password manager for any digital copies, and explore options like steel plates for physical backups that can survive fires or floods.
For bigger holdings, consider multi-signature wallets, which require multiple keys to authorize transactions, adding an extra layer of security.
Avoid Phishing and Social Engineering Attacks
Always double-check the URL of any cryptocurrency website before entering your credentials. Create bookmarks for the sites you regularly use instead of clicking links in emails or search results. Look for the padlock icon indicating a secure connection (though scammers can also use HTTPS), and verify that the domain name is precisely correct, not a close misspelling.
Treat all communications about cryptocurrency investments with extreme skepticism, regardless of the platform. Legitimate companies will never request your private keys, seed phrases, or passwords. If someone claiming to represent a crypto company or exchange contacts you directly, verify their identity through official channels before sharing any information.
The age we live in right now has made recognizing truth increasingly difficult. Advances in AI have made it easier for scammers to create convincing deepfake videos of celebrities or business leaders promoting cryptocurrency scams. Be skeptical of any video promoting high-return investment opportunities, even if it appears to feature a well-known figure. Verify information through official channels before investing.
Verify Crypto Investments
Before investing in any cryptocurrency project, conduct several steps that we mention below:
- Read the whitepaper. This document should clearly explain the project’s technology, use case, and tokenomics. Vague or poorly written whitepapers are a red flag.
- Verify the team. Research the backgrounds of team members to confirm they have relevant experience and aren’t using stolen or AI-generated photos.
- Check code repositories. Legitimate projects typically have active GitHub repositories where you can see development activity.
- Analyze tokenomics. Understand how tokens are distributed, particularly what percentage is held by the founders and development team.
Checking for Whitepapers, Team Credibility, and Audits
Legitimate projects have in-depth whitepapers that explain their technology in detail. The teams behind these projects have verifiable identities and relevant experience that can be confirmed through LinkedIn or other professional platforms.
One of the most famous examples is the Bitcoin whitepaper by the mysterious Satoshi Nakamoto, the first crypto whitepaper ever published that served as a blueprint for all that followed.
For projects involving smart contracts, check if the code has been audited by reputable security firms like CertiK, Quantstamp, or Trail of Bits. These audits can identify vulnerabilities that might put your investment at risk.
Using Blockchain Explorers to Track Transactions
Blockchain explorers like Etherscan (for Ethereum), Blockchair (for multiple blockchains), or Solscan (for Solana) allow you to verify transactions and examine token contracts. Before investing, check if the project’s smart contract has been verified on these platforms and look for any suspicious transaction patterns, such as large transfers to exchanges that might indicate developers selling off their holdings.
What to Do If You Get Scammed
If you’ve fallen victim to a cryptocurrency scam, report it to the appropriate authorities. Here is the list:
- FBI Internet Crime Complaint Center (IC3): The primary U.S. agency for reporting cyber crimes, including cryptocurrency scams.
- Securities and Exchange Commission (SEC): If the scam involved investment fraud or securities violations.
- Commodity Futures Trading Commission (CFTC): For scams involving Bitcoin and other cryptocurrencies traded as commodities.
- Federal Trade Commission (FTC): Particularly for consumer-oriented scams.
If you are outside the U.S., contact your country’s financial regulators. Also, you need to file a police report in your jurisdiction, which may be necessary for insurance claims.
Include as much detail as possible in your report, including wallet addresses, transaction IDs, communication records, and screenshots.
Recovering Lost Funds
Unfortunately, the chances of recovering cryptocurrency lost to scams are typically low due to the irreversible nature of blockchain transactions and the pseudonymous nature of cryptocurrency accounts. However, some steps still exist that might help:
- Contact your cryptocurrency exchange immediately if the scam involved a compromised exchange account.
- If you bought cryptocurrency using a credit card, contact your card issuer to see if they can reverse the charges.
- Consider hiring a cryptocurrency investigation firm that specializes in asset recovery, particularly for large losses, though be cautious about potential recovery scams.
- In some cases, exchanges have frozen funds associated with known scams before they could be withdrawn or laundered.
- Class-action lawsuits sometimes result in partial recovery for victims of large-scale scams.
Warning Others to Prevent Further Scams
Sharing your experience can help prevent others from falling victim to the same scam. Start by reporting the incident to specialized crypto scam tracking websites such as CryptoScamDB, which maintain databases of known fraudulent activities.
Next, consider sharing your story on social media, cryptocurrency forums, and relevant subreddits, being careful to omit any sensitive personal details that might compromise your security.
For phishing attempts, submit the scammer’s details to dedicated databases like PhishTank to help improve detection systems.
Finally, if the scam operated through a specific platform or service, make sure to notify that platform’s trust and safety team so they can take appropriate action to protect other users and potentially flag or remove the scammer’s account.
Conclusion
As cryptocurrency continues to gain mainstream adoption, scammers are refining their tactics. The threats range from elaborate Ponzi schemes to fake cryptocurrencies, from influencer-driven pump-and-dump tactics to social engineering attacks – and worse still, they are constantly evolving and becoming more sophisticated.
By understanding the common types of scams and their warning signs, you can significantly reduce your risk of becoming a victim. Remember that legitimate investments never guarantee returns, trustworthy projects maintain transparency, and nobody needs your private keys.
You need to take action to protect your digital assets: enable 2FAs on all accounts, use hardware wallets for significant holdings, verify URLs before logging in, and thoroughly research projects before investing. If you encounter a scam, report it immediately to the appropriate authorities and share your experience to protect others.
FAQs
What is the most common type of crypto scam?
Investment scams are the most common, according to the FBI. These include Ponzi schemes, fake ICOs, and fraudulent trading platforms that promise high returns with little or no risk. Phishing attacks targeting exchange credentials and wallet keys are also extremely common.
How can I tell if a crypto investment is a scam?
Watch for warning signs like guaranteed returns or very high interest rates, pressure to act quickly, vague technical claims, unverifiable team members, excessive marketing with little substance, limited information about fund usage, and inability to sell tokens or withdraw funds.
Can I recover stolen cryptocurrency?
Recovery is difficult but not always impossible. Because blockchain transactions are irreversible, direct recovery usually isn't an option unless funds remain in an exchange willing to freeze the account. Law enforcement agencies sometimes recover stolen cryptocurrency during investigations, but this typically takes years and often results in only partial recovery.
Are there any tools to check for scam crypto projects?
Several resources can help identify potential scams. Sites like CoinMarketCap and CoinGecko include trust scores and security audits, while Token Sniffer and RugDoc scan smart contracts for vulnerabilities. Scam Alert and CryptoScamDB maintain databases of reported scams, and browser extensions like MetaMask's phishing detector warn about known fraudulent websites. However, no tool is foolproof, and fundamental research remains essential.
How can I report a crypto scam?
Report cryptocurrency scams to the FBI's Internet Crime Complaint Center (IC3) at ic3.gov, the FTC at ReportFraud.ftc.gov, the SEC at sec.gov/tcr, or the CFTC at CFTC.gov/complaint. Also, contact the cryptocurrency exchange or wallet provider involved and your local law enforcement. Include as much information as possible, such as wallet addresses, transaction IDs, screenshots, and communication records.
What should I do if I suspect a phishing attempt?
If you receive a suspicious message potentially phishing for your cryptocurrency credentials, don't click any links or download attachments. Report the attempt to the legitimate company being impersonated and to anti-phishing organizations like PhishTank. Block the sender and mark the communication as spam. If you've already clicked a link, immediately change passwords on any legitimate cryptocurrency accounts, preferably from a different device.
Are celebrity-endorsed crypto projects legit?
Celebrity endorsements don't prove legitimacy. Many celebrities promote cryptocurrencies without understanding the projects or disclosing their compensation. Some have even had their identities used without permission. Always conduct your own research regardless of who appears to be promoting a project, and verify that the endorsement comes from the celebrity's official channels.
How do scammers use deepfake technology in crypto scams?
These deepfake videos typically circulate through social media or fake news websites. Always verify information through official channels, and remember that legitimate businesses and celebrities rarely promote cryptocurrency giveaways requiring you to send funds first.
Is it safe to store my crypto on an exchange?
Storing cryptocurrency on reputable exchanges is relatively safe for active trading but comes with risks. Exchanges can be hacked, face technical issues, or collapse (as with FTX in 2022). For long-term storage or large amounts, hardware wallets offer much better security. If using exchanges, choose established platforms with strong security records, enable all security features, and consider splitting holdings across multiple reputable platforms.